In this post, we will learn how to setup Traefik v2 on ECS with built in LetsEncrypt SSL.
Before I start, I would like to mention that Traefik is awesome reverse proxy & load balancer.
Steps which we will follow:
- Build docker image for Traefik on our local machine
- Push it on Amazon’s Elastic Container Registry (ECR)
- Use pushed image in Task Definition to run Service & Task for Traefik.
Build docker image for Traefik on our local machine
Dockerfile
FROM alekitto/traefik-alpine
COPY traefik_ecs.yaml /etc/traefik/traefik.yaml
RUN touch /etc/traefik/acme.json
RUN chmod +x /etc/traefik/acme.json
traefik_ecs.yaml
## Static configuration
entryPoints:
web:
address: ":80"
http:
redirections:
entryPoint:
to: websecure
scheme: https
websecure:
address: ":443"
http:
tls:
certResolver: myresolver
api:
dashboard: true
providers:
ecs:
exposedByDefault: true
autoDiscoverClusters: false
clusters:
- YOUR_ECS_CLUSTER_NAME
region: YOUR_AWS_REGION
accessKeyID: "YOUR_AWS_ACCESS_KEY_ID"
secretAccessKey: "YOUR_AWS_SECRET_ACCESS_KEY"
certificatesResolvers:
myresolver:
# Enable ACME (Let's Encrypt): automatic SSL.
acme:
email: "YOUR_EMAIL"
storage: "acme.json"
# CA server to use.
# Uncomment the line to use Let's Encrypt's staging server,
# leave commented to go to prod.
#
# Optional
# Default: "https://acme-v02.api.letsencrypt.org/directory"
#
# caServer: "https://acme-staging-v02.api.letsencrypt.org/directory"
# Use a TLS-ALPN-01 ACME challenge.
#
# Optional (but recommended)
#
# tlsChallenge:
httpChallenge:
# EntryPoint to use for the HTTP-01 challenges.
#
# Required
#
entryPoint: web
Now follow these steps to build docker image and push on Elastic Container Registry(ECR)
* Install AWS CLI https://aws.amazon.com/cli/ to execute these steps
export AWS_REGION='YOUR_AWS_REGION'
export AWS_ACCOUNT_ID='YOUR_ACCOUNT_ID'
export ECR_REPO_NAME='YOUR_REPO_NAME'
(aws ecr create-repository --repository-name $ECR_REPO_NAME) || true
eval $(aws ecr get-login --no-include-email --region eu-central-1)
docker build -t $ECR_REPO_NAME:\latest .
docker tag $ECR_REPO_NAME:\latest $AWS_ACCOUNT_ID.dkr.ecr.$AWS_REGION.amazonaws.com/$ECR_REPO_NAME:\latest
docker push $AWS_ACCOUNT_ID.dkr.ecr.$AWS_REGION.amazonaws.com/$ECR_REPO_NAME:\latest
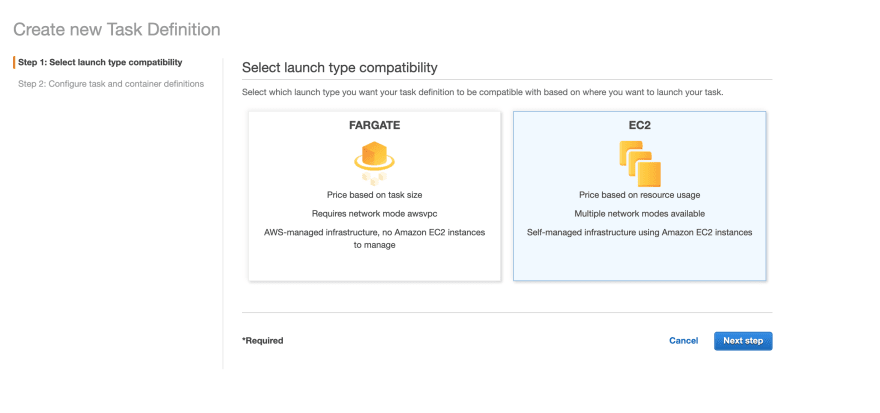
Create task definition to run task from image pushed on ECR




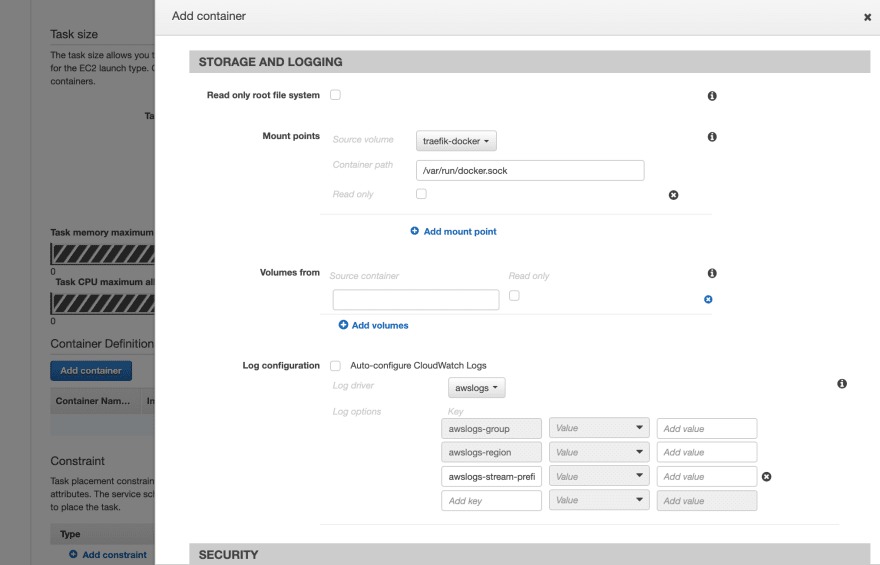

DOCKER LABELS
traefik.http.routers.dashboard.middlewares auth
traefik.http.middlewares.auth.basicauth.users anilmaurya:$apr1$1ktoln283782378923T43el/
traefik.http.routers.dashboard.rule Host(`example.com`) && (PathPrefix(`/api`) || PathPrefix(`/dashboard`))
traefik.http.routers.dashboard.service api@internal
Generate token for basic auth from this site https://hostingcanada.org/htpasswd-generator/
Create one service and run this traefik task definition, after traefik is running we need to add Docker labels to the containers running in same cluster.
Example Docker labels:
traefik.http.routers.app.rule Host(`example.com`)
traefik.http.services.app.loadbalancer.server.port 3000
Conclusion
Github: source code link.
App can be accessed on https://example.com with SSL certificate from Lets Encrypt
traefik dashboard can be accessed on https://example.com/dashboard
Summary:
In this blog, we shed light on how Middleman is a true choice for the developers to add static content. Here is the link for the Demo application for further exploration. Hit the Github link.
** Replace example with your DNS.

